Technology has come a long way, from the creation of mobile phones to the development of AI. We have welcomed technological advancements that make our daily lives easier, and this is something that everyone must accept.
Under the cloak of artificial intelligence now stands a brand new system, and it can recognise people just by looking at them. Face recognition has revolutionised the identification process, and now all the major players use it to ensure their own safety.
What we call “facial recognition” is a method of verifying or establishing a person’s identity by analysing facial features. People in photos, videos, or in real time can all be identified with the help of facial recognition systems. One type of biometric security is facial recognition. In addition to retina and iris scanning, voice recognition and fingerprint scanning are also common biometric technologies. There is growing interest in applying the technology outside of security and law enforcement.
FaceID, which is used to unlock iPhones, has brought face recognition technology to the attention of a large number of people (however, this is only one application of face recognition). In most cases, the process of determining an individual’s identity through facial recognition does not involve consulting a large database of photographs. Instead, it merely identifies and acknowledges one person as the sole owner of the device, while restricting access to other people.
In contrast to any other method of identification, face recognition first determines the distinctive characteristics of an individual’s face and then compares those characteristics to a pre-existing library of photographic images. Face shapes can be detected and identified by sensors based on factors such as the colour of the iris, the shape of the nose, and so on. When trying to determine the identity of a human face, it is necessary to focus on certain distinguishing features, such as the jaw, cheekbones, face shape, and so on. Verification of the face takes place once an image in the database produces a match with the face of the individual in question.
The non-contact characteristic of this solution makes the identification and verification of a person’s identity much simpler than it would be with any other identification system, and it also requires less processing than those systems do.
Computer algorithms are used by face recognition systems to zero in on particular characteristics that are unique to an individual’s appearance. These characteristics, such as the distance that separates the eyes or the contour of the chin, are then converted into a mathematical representation and compared to the information that has been compiled on other people’s faces in a database used for face recognition. The information that pertains to a specific individual’s face is commonly referred to as a face template. A face template is different from a photograph in that it is intended to only include specific details that can be used to differentiate one face from another.
It is essential, when conducting research on a face recognition system, to pay close attention to both the “false positive” rate and the “false negative” rate. This is because there is almost always a trade-off between the two. For instance, if you are using face recognition to unlock your phone, it is preferable that the system not correctly identify you on occasion (this is referred to as a “false negative”) rather than incorrectly identifying other people as you and allowing those other people access to your phone (false positive). The system should be designed to have as few false positives as possible if the result of a misidentification is that an innocent person goes to jail (for example, if a misidentification occurs in a mugshot database).
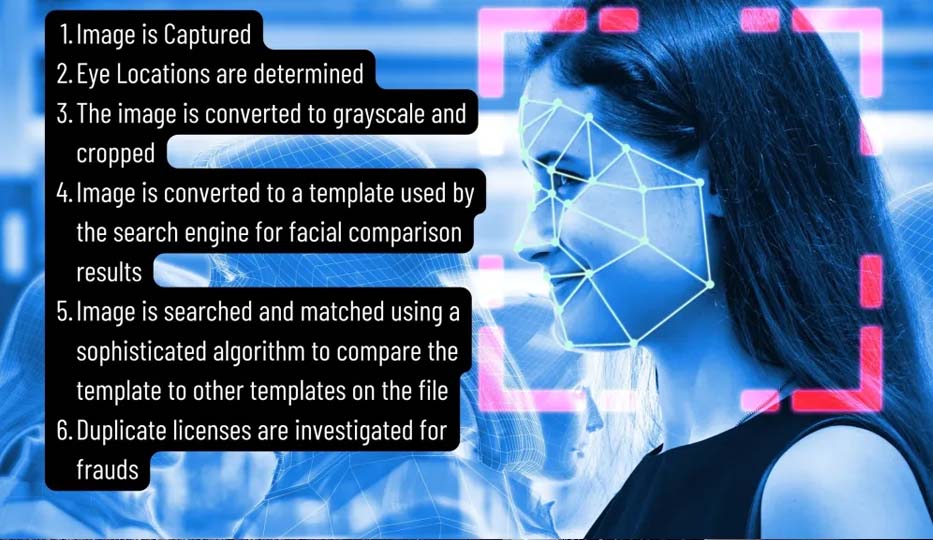
Hence, we can say that in addition to allowing users to unlock their phones, facial recognition can also be used to match the faces of people walking in front of specialised cameras to photographs of individuals who are on a watch list. The images that are included on the watch lists can originate from anywhere, including our own social media accounts, and they can contain pictures of anyone, including people who are not suspected of having committed any wrongdoing. Although the specifics of how facial technology systems work can vary, in general, they function as follows:
Face recognition is becoming an increasingly common tool for use in the day-to-day operations of law enforcement agencies. The arrestees’ mugshots are entered into local, state, and federal face recognition databases after being collected by the police from those who have been detained. After an arrestee’s photograph has been taken, that photograph will be stored in one or more databases, and it will be scanned whenever the police conduct another criminal search.
It is then possible for law enforcement to query these massive mugshot databases in order to identify individuals in photographs obtained from social media, CCTV, traffic cameras, or even photographs that law enforcement officers themselves have taken in the field. In addition, “hot lists” of people suspected of engaging in illegal activity can be compared in real time with people’s faces.
Mobile face recognition enables law enforcement officers to make use of smartphones, tablets, and other portable electronic devices to take a photograph of a driver or pedestrian in the field, and then immediately compare that photograph to one or more face recognition databases in order to make an identification attempt.
Face recognition technology has been put to use in a variety of settings, including airports, border crossings, and major sporting events like the Olympic Games. Face recognition technology may also be utilised in privately owned establishments such as shops and sports arenas; however, the regulations governing its use in the private sector may vary.
In the most important establishments and workplaces, a facial biometrics system has been implemented as a security measure to ensure that there is no room for any kind of vandalism. The use of this kind of software eliminates any and all opportunities for error on the part of humans and represents a significant assistance. Within a matter of seconds, the software is capable of geometric and photometric recognition solely based on a collection of algorithms.
Because it is so simple to implement and makes use of relatively inexpensive technology, this facial biometrics system has quickly become the industry standard for recognition software. Its non-contact nature is the best thing about it in the sense that a person can be recognised through facial recognition even in a crowded place as long as his../images are saved in the database. This makes it possible for a person to be recognised even if they are hiding.
Access to information can be further restricted and limited using facial recognition, which benefits only those who own the information.
The use of facial recognition has made verification relatively simpler, requiring little to no equipment and allowing users to gain access to a great deal of information in a matter of minutes.
Improved safety and protection: Facial recognition technology can be used by the government to assist in the identification of terrorists and other criminals. Facial recognition can be used on a personal level as a security tool for locking personal devices as well as for personal surveillance cameras.
A decrease in criminal activity: The use of facial recognition technology makes it simpler to apprehend trespassers, thieves, and burglars. Even the simple awareness of the existence of a face recognition system has the potential to act as a deterrent, particularly in the case of less serious offences. In addition to the advantages of having physical security, there are also advantages to having strong cybersecurity. Face recognition technology can be used to access company computers, which eliminates the need for companies to use passwords. In principle, the technology cannot be broken into because there is nothing that can be taken or altered, as is the case with a password.
Taking prejudice out of the stop-and-search system: A source of controversy for the police is the public’s concern over unjustified stops and searches; facial recognition technology could make the process more efficient. Face recognition technology could help reduce the possibility of bias and reduce the number of times law-abiding citizens are stopped and searched by the police. This would be accomplished by using an automated rather than a human process to single out suspects from large crowds.
The convenience is increased: Customers will soon be able to pay for purchases in stores simply by presenting their face rather than having to pull out their credit cards or cash. This capability will become available as facial recognition technology becomes more widespread. This may shorten the amount of time spent waiting in checkout lines. Facial recognition provides a verification process that is rapid, hands-free, and unobtrusive because, unlike fingerprinting and other security measures, it does not require the user to make physical contact with a device in order to obtain an accurate reading. This is particularly useful in the post-COVID era.
A quicker processing time: The fact that it takes less than a second to identify a person based on their face is an advantage for businesses that implement facial recognition technology. In this day and age of sophisticated hacking tools and online attacks, businesses require technologies that are both secure and quick. Verification of a person’s identity can be carried out in a prompt and effective manner thanks to facial recognition technology.
Integration with a variety of other technological platforms: The majority of facial recognition solutions are compatible with the majority of different types of security software. In point of fact, it is very simple to incorporate. This reduces the amount of additional investment that will be necessary to put it into effect.